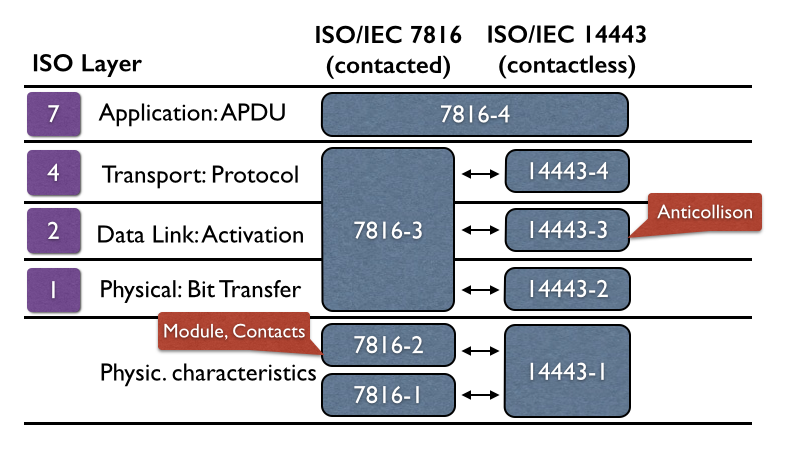
This Java sample code describes the Java Smart Card I/O API used to get access to a common smart card. It demonstrates the communication with smart cards using APDUs specified in ISO/IEC 7816-4. It thereby allows Java applications to interact with applications running on the smart card.
The Application Programming Interface (API) for the Java Card technology defines the communication protocol conventions by which an application accesses the Java Card Runtime Environment and native services. To assure interoperability, the Java Card API is compatible with formal international standards, such as ISO/IEC 7816, and industry-specific standards, such as EMVCo’s EMV standards for payment, and ESI/3GPP standards for UICC/SIM cards.
In this Java sample code the command GET CHALLENGE is used to demonstrate a simple command sent to smart card. At the beginning of the communication protocol all registered card readers (terminals) are listed and the first one is selected to get connected with the smart card. Once the connection is established the command GET CHALLENGE is sent to the card and a random sequence of 8 bytes is returned as response.
And here is the code snippet of this sample:
// Show the list of all available card readers:
TerminalFactory factory = TerminalFactory.getDefault();
List<CardTerminal> terminals = factory.terminals().list();
System.out.println("Reader: " + terminals);
// Use the first card reader:
CardTerminal terminal = terminals.get(0);
// Establish a connection with the card:
Card card = terminal.connect("*");
System.out.println("Card: " + card);
CardChannel channel = card.getBasicChannel();
ResponseAPDU r = channel.transmit(new CommandAPDU(0x00, 0x84, 0x00, 0x00, 0x08));
String hex = DatatypeConverter.printHexBinary(r.getBytes());
System.out.println("Response: " + hex);
// disconnect card:
card.disconnect(false);
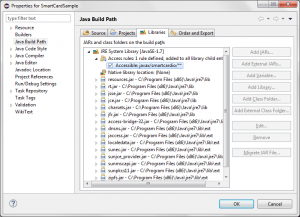
If you want to use this sample in your IDE, e.g. Eclipse, keep in mind that you must access the Java Card API in a manually way. In Eclipse you can do this in project properties. Add the following access rule to the java build path: javax/smartcardio/** This allows you do access additional methods for smart cards in Java. You can find this adjustment in the following screenshot (Eclipse):
Eclipse – Project properties to access Java Card API for Java code sample