Introduction
There is an update of BSI technical guideline TR-03105 Part 5.1 available. The new version 1.4 of this test specification for inspection systems with EACv1 is focusing on PACE (including PACE-CAM) and LDS 1.8.
The new version of TR-03105 is now available in new BSI layout. Additionally, there are some minor editorial changes and updated references (e.g. new Doc9303 is referenced).
New test cases in TR-03105 Part 5.1
The Standard Inspection Procedure (SIP) includes now also PACE and there is a new configuration specified for default PACE passport.
New test cases for PACE/SAC
Here is a list of new test cases, added in TR-03105 5.1 to test PACE, including PACE-CAM:
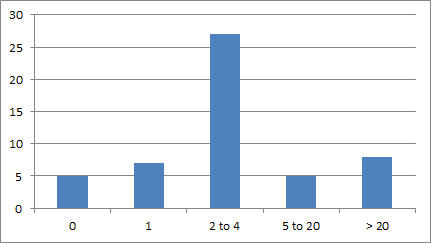
- ISO7816_G_01: Correct execution of PACE protocols
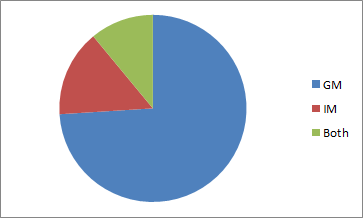
- ISO7816_G_02: Check supported standardized domain parameters with Generic Mapping
- ISO7816_G_03: Check supported standardized domain parameters with Integrated Mapping
- ISO7816_G_04: Check supported algorithms
- ISO7816_G_05: Check PACE with additional entries in SecurityInfos
- ISO7816_G_06: Check selection of standardized Domain Parameters and algorithms
- ISO7816_G_07: EF.CardAccess contains two PACEInfo and PACEDomainParameter
- ISO7816_G_08: Abort PACE because of SW error code during MSE:Set AT
- ISO7816_G_09: Error on the nonce – Value modifications after first General Authenticate
- ISO7816_G_10: Error on General Authenticate step 1 command
- ISO7816_G_11: Error on General Authenticate step 1 command – bad tag (use 90h instead of 80h)
- ISO7816_G_12: Error on General Authenticate step 2 command
- ISO7816_G_13: Error on General Authenticate step 2 command bad tag (use 92h instead of 82h)
- ISO7816_G_14: Abort PACE because of error in GA step 2 (GM)
- ISO7816_G_15: Abort PACE because of error in GA step 2 (IM)
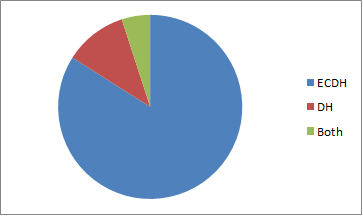
- ISO7816_G_16: Error in General Authenticate step 2 command – error on mapping data – all ECDH public key components
- ISO7816_G_17: Error in General Authenticate step 2 command – error on mapping data – all DH public key components
- ISO7816_G_18: Error in General Authenticate step 3 command
- ISO7816_G_19: Error in General Authenticate step 3 command – bad tag (use 94h instead of 84h)
- ISO7816_G_20: Abort PACE because of error in GA step 3
- ISO7816_G_21: Error on General Authenticate step 3 command – error on ephemeral public key – all ECDH public key components
- ISO7816_G_22: Error on General Authenticate step 3 command – error on ephemeral public key – all DH public key components
- ISO7816_G_23: Abort PACE because of identical ephemeral public keys
- ISO7816_G_24: Error on General Authenticate step 4 command
- ISO7816_G_25: Error on General Authenticate step 4 command – bad tag (use 96h instead of 86h)
- ISO7816_G_26: Abort PACE because of error in GA step 4
- ISO7816_G_27: Abort PACE because of TLV error on EF.CardAccess
- ISO7816_G_28: Abort PACE because of incorrect parameterId in PACEInfo
- ISO7816_G_29: PACE-CAM with missing tag 8Ah but correct ECAD
- ISO7816_G_30: PACE-CAM with incorrectly encoded tag ECAD (no octet string)
- ISO7816_G_31: PACE-CAM with wrong tag ECAD
- ISO7816_G_32: PACE-CAM with wrong tag 8Ah (use 8Bh) but correct ECAD
- ISO7816_G_33: PACE-CAM with correct tag 8Ah but missing ECAD
- ISO7816_G_34: PACE-CAM with Passive Authentication
- ISO7816_G_35: Return additional tag 8Ah during PACE-GM
- ISO7816_G_36: Use invalid OID for PACE-CAM in EF.CardAccess
- ISO7816_G_37: Use EF.CardAccess with PACEInfo only for PACE-CAM (no GM or IM)
- ISO7816_G_38: Use DG14 without SecurityInfo during PACE-CAM
- ISO7816_G_39: Use EF.CardSecurity with wrong ChipAuthenticationPublicKeyInfo during PACE-CAM
- ISO7816_G_40: Use EF.CardSecurity without ChipAuthenticationPublicKeyInfo during PACE-CAM
- ISO7816_G_41: Check supported standardized domain parameters with Chip Authentication Mapping
New test cases for LDS 1.8
Here is a list of new test cases, added in TR-03105 5.1 to test LDS 1.8:
- LDS_A_10: EF.COM with LDS Version 1.8
- LDS_H_86: EF.SOD with LDS Version 1.8
- LDS_H_87: Security Object with LDS Version 1.8 but with wrong version number
- LDS_H_88: Security Object with LDS Version 1.7 but version number 1
- LDS_H_89: EF.SOD with future LDS Version 1.9
Adapted test cases in TR-03105
Here is a list of modified test cases in TR-03105 5.1:
- In chapter 7.1.2 the OIDs for plain signatures are corrected.
- ISO7816_D_06: Added second public key with key reference FE in EF.DG14
- ISO7816_D_15: Use configuration of D_06 to assure the use of wrong key reference
- ISO7816_F_02: Added signature algorithm (ECDSA with SHA1) in EF.DG14 to fulfil requirements
- ISO7816_F_08: Changed expected results in transfer interface: TA and CA might not be performed
- LDS_A_06: Correction in EF.COM where Unicode Version 5 must be encoded
- LDS_D_08: The referenced invalid format owner (0102) is used by JTC1/SC27 IT Security Techniques (see www.ibia.org/base/cbeff/biometric_org.phpx). So the referenced invalid format owner was changed to ’87 02 01 FF’.
- LDS_E_07: The referenced invalid format owner (0102) is used by JTC1/SC27 IT Security Techniques (see www.ibia.org/base/cbeff/_biometric_org.phpx). So the referenced invalid format owner was changed to ’87 02 01 FF’.
- LDS_H_04: Correction in EF.SOD where RSASSA-PKCS1_v15 must be used
- LDS_H_50: The serial number is mandatory, so expected result was changed to “FAIL”
Next steps
The version 1.4 of BSI TR-03105 Part 5.1 is a backport of ISO18745-4. Until the ISO test specification is under construction and not released, TR-03105 can be used as an interims version for testing inspection systems using PACE/SAC.